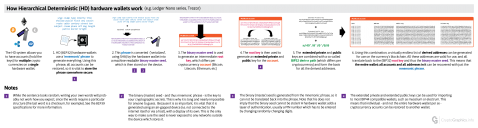
HD Wallets
Hierarchical Deterministic (HD) wallets – such as the Ledger Nano series, Trezor and Carbon wallets – allow you to have accounts (e.g. hold the keys) for multiple crypto currencies on a single wallet. Here’s how they work.
Mnemonic phrase
- HD (BIP32) hardware wallets use a ‘mnemonic’ phrase to generate everything; all accounts can be restored using this phrase, so it is vital to store the phrase somewhere secure.
- This phrase is converted (’serialized’, using SHA) by the hardware wallet into a machine-readable binary master seed, which is then stored on the device.
Root key
- The generated binary master seed is used to generate an intermediate root key, which differs per cryptocurrency account (Bitcoin, Litecoin, Ethereum, etc).
- The root key is then used to generate an extended private and public key for the account.
Derived addresses
Using this combination, a virtually endless list of derived addresses can be generated for use on the currency’s blockchain. All these addresses are valid for use, and all translate back to the (BIP32) root key and thus the binary master seed. This means that the entire wallet; all accounts and all addresses in it can be recovered with just the mnemonic phrase.
A great interactive way to see this system in action can be seen here.
Notes
- While the sentence looks random, writing your own words will probably not work how you expect, since the words require a particular structure (the last word is a checksum). See the BIP39 specifications for more information.
The binary (master) seed – and thus mnemonic phrase – is the key to your cryptographic secrets. This is why it is long and nearly impossible for anyone to guess. Because it is so important, it is vital that it is generated using an air-gapped device (i.e. not connected to the internet itself or via a host), with a display of its own. This is the only way to make sure the seed is never exposed to any networks outside the device which stores it.
The binary (master) seed is generated from the mnemonic phrase, so it can not be translated back into the phrase. Note that his does not imply that the binary seed cannot be stolen! To protect it, a hardware wallet adds a layer of authentication, usually a PIN number which has to be entered by changing randomly changing digits.
Some wallets offer an extra layer, allowing you to combine the mnemonic phrase with another, additional, textstring/passphrase.
The extended private and extended public keys can be used for importing to most BIP44 compatible wallets, such as mycelium or electrum. This means that individual – and not the entire hardware wallet per se – cryptocurrency acounts can be restored to another wallet.